To avoid fake tech support calls and pop-up virus warnings, stay alert for urgent messages asking for immediate action or payment, and never click links or share remote access details. Verify support contacts through official websites, and use trusted security software to scan your device. If you suspect a scam, disconnect from the internet and report it to authorities. Protect yourself by understanding common tactics—keep exploring to learn how to stay safe from these scams.
Key Takeaways
- Never click on suspicious pop-ups; close them using task manager or restart your device instead.
- Verify support contact details through official company websites before seeking help.
- Avoid sharing personal or payment information during unsolicited calls or pop-up alerts.
- Be cautious of urgent language and fake warnings that pressure immediate action or payments.
- Report scam calls, emails, and pop-ups to authorities to help prevent others from falling victim.
Top picks for "scam alert avoid"
Open Amazon search results for this keyword.
As an affiliate, we earn on qualifying purchases.
Recognizing Common Signs of Fake Tech Support Calls
Fake tech support calls often start with aggressive or urgent messages that pressure you into acting quickly. Scammers may claim your computer is infected or about to crash, urging you to click links or provide personal info. Be cautious if you receive phishing emails that seem suspicious or come from fake websites designed to look legitimate. These sites often mimic real tech support pages but have subtle differences, like misspelled URLs or unusual layouts. If you’re prompted to share remote access or pay fees unexpectedly, it’s a red flag. Authentic companies don’t typically call out of the blue or demand immediate payment. Recognizing these signs helps you avoid falling victim to scams that rely on creating panic and confusion. Staying informed about network security best practices can help you identify and avoid these threats more effectively. Remember that scammers often use social engineering tactics to manipulate your trust and induce hurried decisions. Being aware of projector technology features and typical specifications can also help you discern legitimate support from scams. Additionally, understanding common cybersecurity vulnerabilities can empower you to recognize genuine communications and avoid fake alerts. Being familiar with antivirus software behaviors and alerts can further aid in detecting potential scam attempts. Stay alert and verify before taking any action.
Typical Tactics Used by Scammers to Deceive Users

Scammers often display fake phone numbers to make their calls seem legitimate and gain your trust. They use alarmist language to create a sense of urgency, pushing you to act quickly without thinking. Additionally, they throw around persuasive technical jargon to sound convincing and mask their true intentions. To protect yourself, it’s important to recognize trusted workspace practices and stay cautious when encountering suspicious messages. Being aware of common scam tactics, including the use of deceptive marketing techniques, can help you identify and avoid these deceptive schemes before they cause harm. Recognizing the impact of cookies and how they are used can also help you maintain better control over your online privacy and security. Understanding how Rhythm Failure produces uplifting music like “Blue Skies and Lemonade” can also improve your awareness of genuine sources of positivity online.
Fake Phone Numbers Displayed
When you see unfamiliar phone numbers pop up on your caller ID, it’s often part of a scammer’s tactic to deceive you into trusting their false authority. These scammers use fake phone numbers to appear legitimate, making it harder to identify their true intent. To recognize phone number scams, keep these tactics in mind:
- They spoof local or familiar area codes to seem trustworthy.
- They often change numbers frequently to avoid detection.
- They display numbers that mimic official organizations or support services.
Alarmist Language Used
Alarmist language is a common tactic scammers use to make their messages seem urgent and credible. They often send email scams or display fake alerts that threaten your device’s security or personal data. These messages create a sense of panic, urging you to act immediately without thinking. For example, a fake alert might warn you that your computer is infected or that your bank account is compromised. Scammers rely on this fear to get you to call a fake support number, download malicious software, or share sensitive information. Recognizing these tactics is essential. Remember, legitimate companies rarely use urgent language or threats in emails or pop-ups. Staying vigilant about potential vetted threats and verifying the source can help you avoid falling victim to scams. Stay calm, verify the source, and avoid reacting to alarmist messages.
Persuasive Technical Jargon
Persuasive technical jargon is a powerful tool scammers use to convince you that their messages are legitimate. They often use complex, technical-sounding terms to create a false sense of authority, making it hard to distinguish real alerts from scams. To improve your phishing awareness, recognize phrases like “your system has been compromised” or “urgent security update required,” which are designed to trigger panic. Scammers also leverage cybersecurity training to make their language sound credible. Be cautious of: 1. Technical terms that seem out of context or overly complicated 2. Phrases emphasizing immediate action, like “click now” or “verify instantly” 3. Use of official-sounding jargon, such as “virus detection,” “security breach,” or “system vulnerability.” Additionally, scammers often mimic trusted business directories to lend an air of legitimacy to their claims. Recognizing these manipulative language tactics helps you stay alert and avoid falling for fake tech support scams, especially by understanding the persuasive communication techniques used to deceive users. Being aware of deceptive tactics can help you better identify and avoid these scams before it’s too late.
How Pop-Up Warnings Can Trick You Into Action
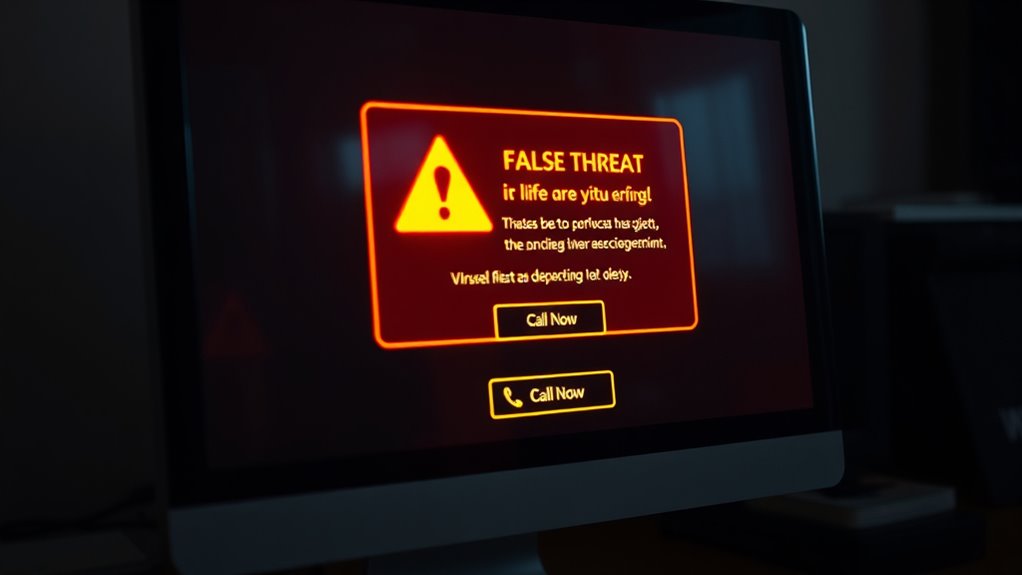
Pop-up warnings can be incredibly convincing, often designed to look like legitimate alerts from your computer or trusted security companies. They use bright colors, urgent language, and official logos to grab your attention. These tactics are part of social engineering, aiming to trick you into taking action without thinking. Sometimes, the pop-up may claim you have a virus or need to call tech support immediately. Be cautious—these messages are often linked to phishing emails or malware. They want you to click a link or provide personal info. Always verify the source before acting. Remember, real security alerts won’t ask for personal info or push you to call a number immediately.
| Fake Alert | Phishing Trick | Immediate Action Needed |
|---|---|---|
| Looks urgent | Tries to scare | Calls or clicks link |
| Mimics real alerts | Steals info | Downloads malware |
| Uses logos | Social engineering | Panic drives response |
The Importance of Verifying Tech Support Contacts

Always verify the contact details of any tech support before trusting them. Use official websites or trusted sources to confirm their phone numbers and email addresses. Recognizing legitimate support channels helps you avoid scams and keeps your devices secure. Being aware of common scams and fraud tactics can further protect you from falling victim to fake tech support calls. Additionally, understanding water safety practices can prevent accidents when dealing with water-related devices or environments. Staying informed about device security measures can also help in identifying genuine support services and safeguarding your personal information. Educating yourself about cybersecurity best practices further enhances your ability to detect and avoid fraudulent support attempts.
Confirm Official Contact Details
Verifying the contact details of your tech support provider is a crucial step in avoiding scams. Scammers often send phishing emails or create fake antivirus alerts to trick you into revealing personal information or granting remote access. To stay safe, confirm you verify contact details through official sources. Additionally, Gold IRA markets emphasize secure connections and verified support channels to prevent similar scams in the digital age. Always check the official website or contact number listed on the company’s legitimate platform to ensure authenticity and cybersecurity awareness. Being aware of necessary cookies and their role can help you recognize suspicious online activities related to fake support calls.
Recognize Legitimate Support Channels
Since scammers often impersonate legitimate support channels, verifying you’re contacting the real provider is essential. Be cautious of phishing emails that appear to come from trusted companies, but instead direct you to fake websites designed to steal your information. Always check the website URL carefully—official sites usually have secure connections (https://) and match the company’s official domain. Avoid clicking links in unsolicited emails or pop-up messages that claim urgent support needs. Instead, go directly to the company’s official website or call their verified support number. Legitimate tech support teams won’t pressure you to act immediately or request remote access without proper verification. Recognizing these signs helps you confirm you’re dealing with authentic support channels and avoids falling victim to scams. Additionally, being aware of common security zone info can help you better identify trustworthy sources. Remember that identity theft protection strategies are vital when dealing with unexpected tech support communications. Always stay informed about scam tactics to better protect yourself from evolving threats.
Safe Practices for Handling Unexpected Virus Alerts

When you see a sudden pop-up claiming your device is infected, it’s essential to stay calm and avoid clicking any links or buttons. These alerts are often fake and designed to prompt malware downloads or phishing emails. To handle these situations safely:
- Close the pop-up using your task manager or restart your device, avoiding interaction with suspicious messages.
- Use reputable security software to scan your system for malware and remove any threats.
- Never provide personal information or payment details in response to unexpected virus alerts. Remember, legitimate companies won’t ask for sensitive info through pop-ups. By remaining cautious, you reduce the risk of falling for scams that rely on fake alerts to steal your data or infect your device.
- Familiarize yourself with air purifier technology and common scams to better recognize legitimate alerts versus fake ones.
Steps to Take If You Suspect a Scam

If you suspect you’ve fallen victim to a scam, acting quickly can prevent further damage. Start by disconnecting your device from the internet to stop any ongoing data transfer. Check your accounts for suspicious activity, especially for signs of identity theft. Change your passwords, using strong, unique combinations, to protect your online privacy. Contact your bank or relevant institutions to report fraud and monitor your finances closely. Keep a record of all suspicious messages or calls. Use the table below to guide your next steps:
| Step | Action | Purpose |
|---|---|---|
| Disconnect from Internet | Turn off Wi-Fi or unplug Ethernet | Prevent data theft |
| Review Accounts | Check for unauthorized activity | Detect potential identity theft |
| Change Passwords | Use complex, unique passwords | Secure online privacy |
| Report Incidents | Contact authorities and banks | Stop scammers and protect assets |
| Save Evidence | Keep logs and messages | Support investigations |
Tools and Software to Protect Against Fake Support Attacks
Protecting yourself from fake tech support scams requires more than just awareness; it calls for effective tools and software that can detect and block malicious activity. These tools help identify phishing email attempts and prevent malware from taking hold. Consider implementing the following:
Using effective security tools is essential to detect and block fake tech support scams.
- Antivirus and anti-malware software with real-time scanning to detect malware removal threats early.
- Email filtering solutions that flag suspicious phishing emails before they reach your inbox.
- Firewall and browser security extensions to block malicious websites and pop-up virus warnings.
These tools work together to fortify your defenses, making it harder for scammers to hijack your device or steal your information. Staying vigilant and utilizing robust software guarantees you’re better protected against fake support calls and virus scams.
What to Do if You’ve Fallen Victim to a Scam

If you realize you’ve been scammed, stay calm and don’t panic. Immediately disconnect from the internet and any contact with the scammer. Then, report the incident to authorities and seek help to protect your information and devices.
Do Not Panic
When you realize you’ve fallen victim to a scam, it’s natural to feel alarmed, but panicking can make the situation worse. Staying calm helps you think clearly and act effectively. To maintain a mindful calm and avoid panic, focus on these steps:
- Take a deep breath and pause before reacting, preventing impulsive decisions.
- Disconnect from the scammer or suspicious links to stop further damage.
- Gather any relevant information, like emails or messages, to report the incident accurately.
Remaining composed allows you to assess the situation realistically, seek proper help, and avoid making rash choices that could worsen the problem. Remember, staying calm is your best defense in these moments.
Disconnect Immediately
As soon as you realize you’ve fallen for a scam, the most important step is to disconnect immediately from the source to prevent further damage. If you suspect phone scams or email fraud, hang up the call or delete the suspicious email right away. Do not click on any links, open attachments, or provide personal information. Cutting off contact stops the scammer from gaining more access or extracting more data from you. Even if you feel pressured to stay on the line or respond, resist. Disconnecting quickly minimizes the risk of malware installation, financial theft, or identity theft. Remember, scammers rely on urgency and manipulation, so taking swift action by cutting the connection is your best defense.
Report and Seek Help
Once you’ve disconnected from the scam, taking the next step to protect yourself is reporting the incident and seeking help. This helps prevent further online scams and alerts authorities to ongoing phishing emails or fake tech support schemes.
- Contact your bank or credit card company if you shared financial info, and monitor your accounts for suspicious activity.
- Report the scam to local authorities and online platforms like the Federal Trade Commission (FTC) or your country’s cybersecurity agency.
- Inform your email provider about phishing emails or suspicious messages to help prevent others from falling victim.
Educating Family and Friends About Tech Support Scams

Educating your family and friends about tech support scams is essential because they are often targeted by scammers who exploit their lack of technical knowledge. Many fall for phishing emails that appear legitimate, unknowingly providing scammers access to their personal information. Others might click on links that initiate malware downloads, compromising their devices. You can help by explaining how scammers pose as legitimate support agents and never ask for remote access or payment upfront. Encourage them to verify any tech support requests directly through official company channels. Remind them to be cautious of unsolicited calls, emails, or pop-up warnings that seem suspicious. Empowering your loved ones with this knowledge helps them recognize scams early and avoid costly mistakes.
Staying Informed: Keeping up With Evolving Scammer Techniques

Staying ahead of scammers requires you to actively monitor how they adapt their techniques. They constantly refine methods like phishing emails or fake antivirus alerts to deceive even cautious users. To keep up, consider these strategies:
- Follow trusted cybersecurity news sources to stay informed about new scam tactics.
- Recognize common signs of phishing emails, such as urgent language or suspicious links.
- Be skeptical of pop-up alerts claiming your device is infected, especially if they promote fake antivirus solutions or request personal info.
Frequently Asked Questions
How Can I Differentiate Between Legitimate and Fake Tech Support Websites?
To differentiate between legitimate and fake tech support websites, you should check website verification and trust indicators. Look for secure connections with “https” and a padlock icon in the URL bar. Verify the website’s domain closely—official sites usually have clear, professional URLs. Trust indicators like contact details, reviews, and official logos can also help. If anything looks suspicious or inconsistent, it’s best to avoid providing personal info or payment details.
Are There Specific Warning Signs That Indicate a Pop-Up Is a Scam?
Think of scam pop-ups as wolves in sheep’s clothing. Look for warning signs like urgent language, spelling errors, or unfamiliar URLs—these are clear scam indicators. If a pop-up cues you to call a number or share personal info, it’s likely a scam. Trust your instincts and close suspicious windows. Never click on links or download attachments from unknown sources, and always verify the legitimacy before taking any action.
What Are the Best Practices for Updating My Device Security Software?
To keep your device secure, regularly update your security software by installing the latest software updates and security patches. Enable automatic updates if possible, so you don’t miss critical fixes. Always download updates from official sources to avoid scams. Staying current guarantees your software can defend against new threats, and security patches fix vulnerabilities hackers might exploit. Make updating a routine part of your device maintenance to stay protected.
Can Scammers Access My Personal Information Through Fake Tech Support Calls?
Did you know that over 30% of phishing scams target personal info? Yes, scammers can access your personal information through fake tech support calls if you’re not careful. They often pretend to be legit, tricking you into revealing sensitive details. Stay vigilant, never share personal info over calls, and verify identities before trusting anyone claiming to offer tech help. Protect yourself from identity theft by staying cautious with unknown callers.
How Often Should I Review and Update My Security Protocols?
You should review and update your security protocols at least quarterly. Make sure you regularly update passwords, especially for sensitive accounts, and enable multi-factor authentication where possible. Continuously monitor your network for unusual activity, which helps catch threats early. Staying proactive by reviewing security measures frequently keeps your data safe from scams and cyberattacks, ensuring your defenses are always current and effective against emerging threats.
Conclusion
Stay one step ahead of scammers, like a lighthouse guiding ships safely through treacherous waters. Trust your instincts and verify before clicking, because these fake support calls and pop-ups are cunning pirates trying to steal your treasure. By staying informed and cautious, you can keep your digital shores secure. Remember, a vigilant mind is your strongest armor—don’t let scammers sail into your safe harbor. Protect your digital world before they strike again.